iRocket
Unlock Endless Possibilities with One-Click Location Changer!
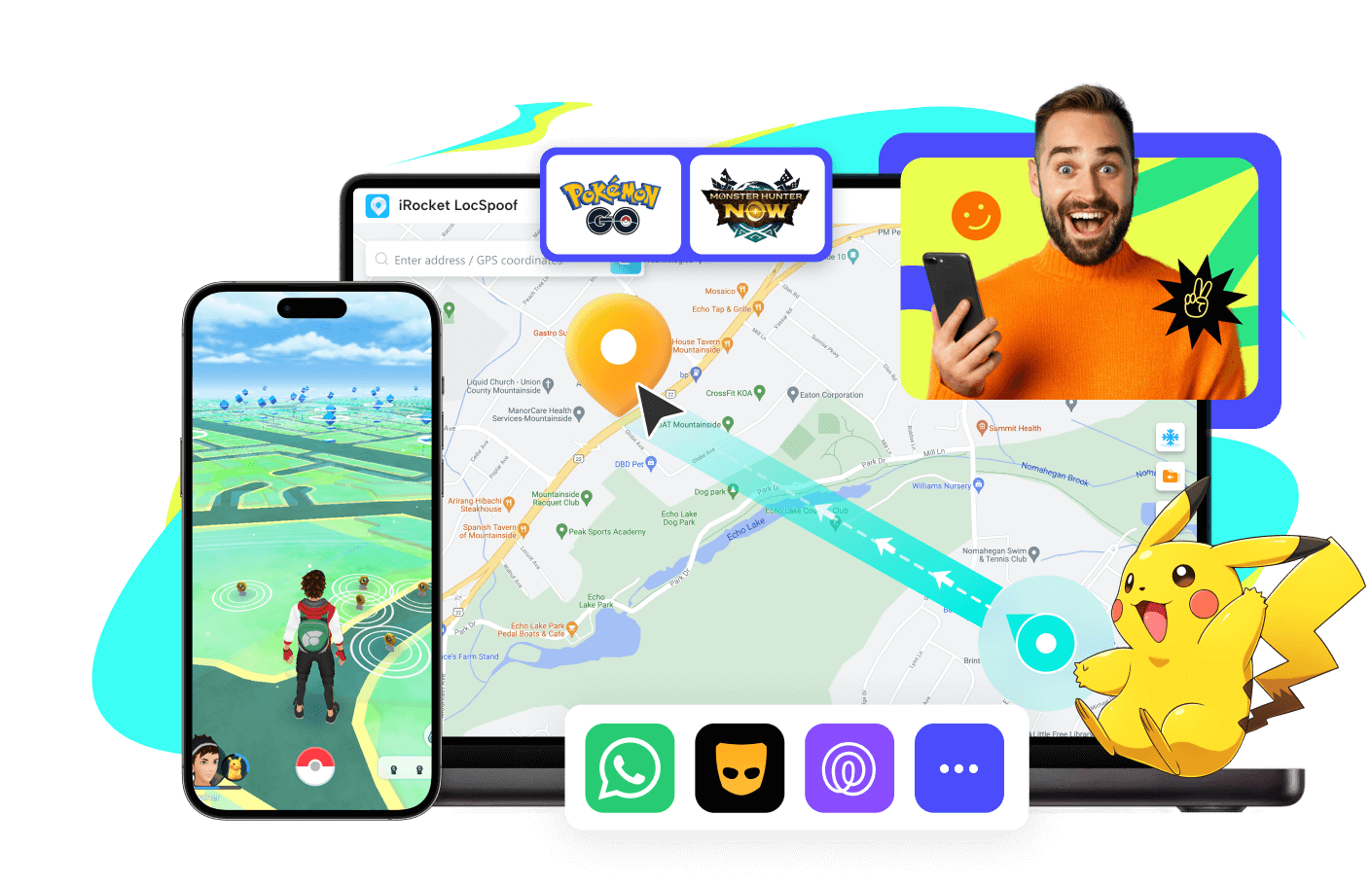
iRocket LocSpoof
Take control of your iOS/Android location at anytime.
- Change your GPS location on iPhone & Android with just one click, no jailbreak or root required.
- Protect your privacy by spoofing your location on social apps like WhatsApp, Tinder, life360 and more.
- Play location-based AR games like Pokémon GO, Monster Hunter now etc. without going outside.
- Simulate realistic GPS motion with custom routes and adjustable speeds for a seamless experience.
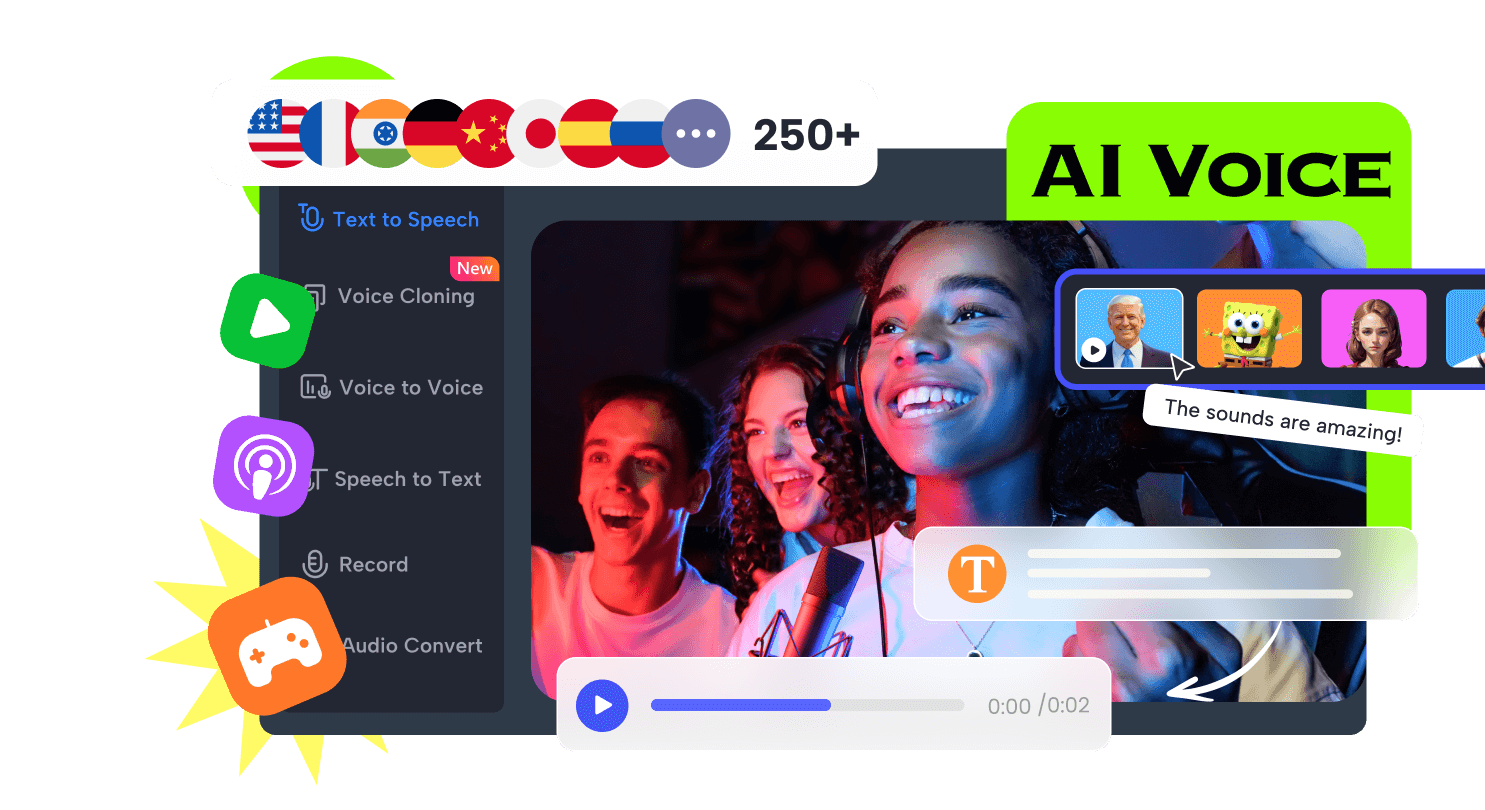
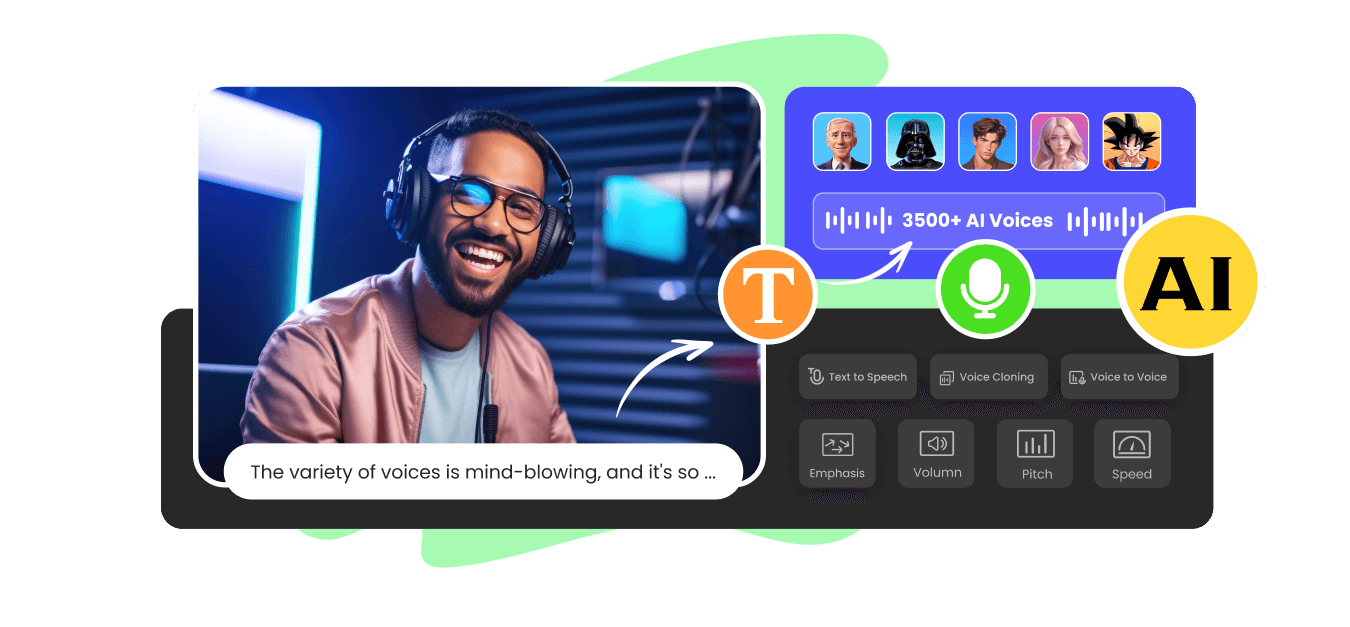
Unleash the Magic of Your Voice with AI Power!
iRocket VoxTalker
Turn text into lifelike voices in any languages.
- Access 3500+ natural-sounding AI voices across 250+ languages and accents, including celebrity and cartoon voices.
- Create personalized voiceovers for videos, podcasts, audiobooks and more with precise voice cloning and tuning.
- Customize voice parameters such as pitch, rate, pauses and emotions to achieve the perfect sound.

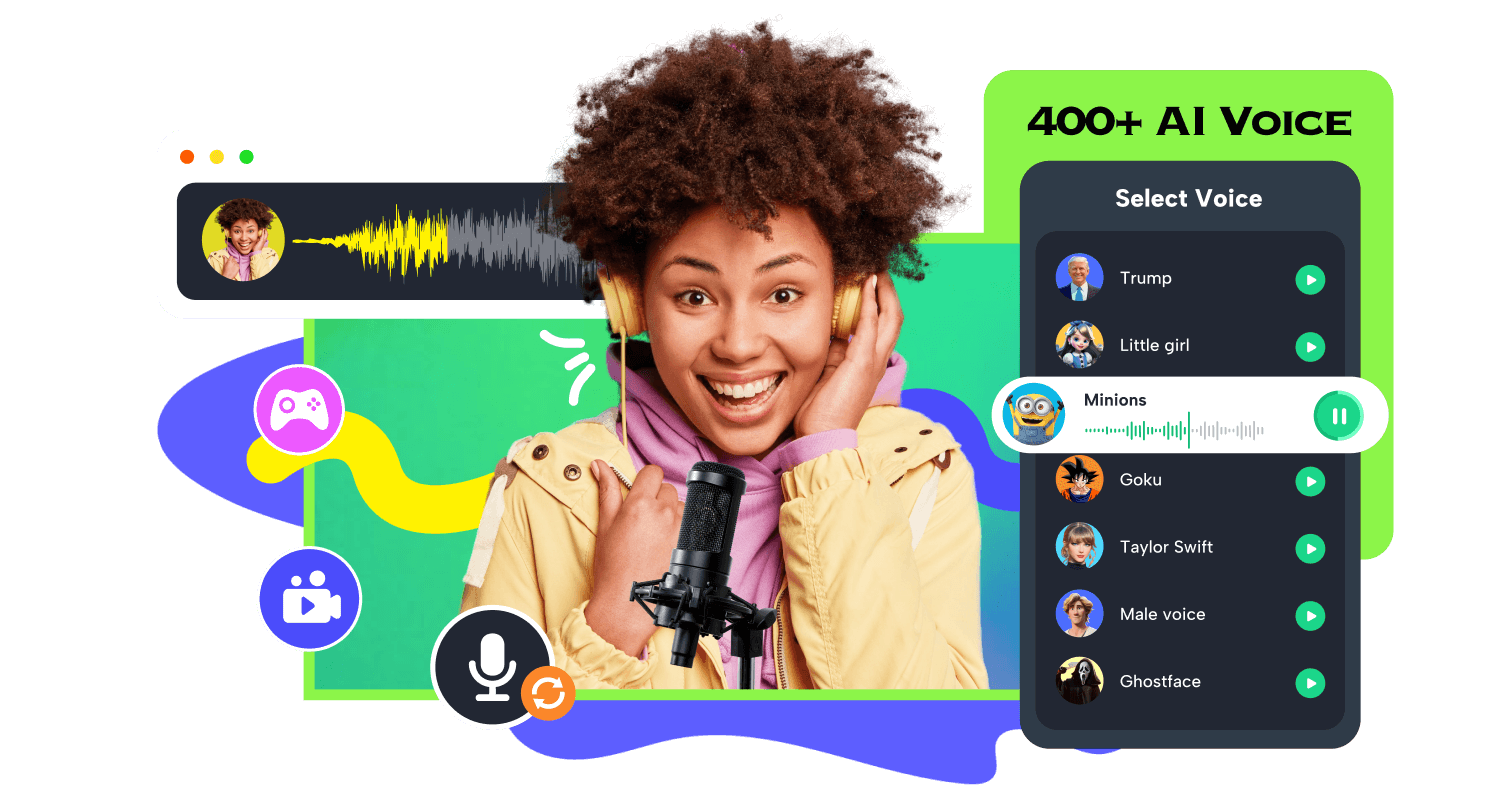
iRocket iCreaVoice
Change voice for gaming, streaming or online-chatting with endless fun.
- Change your voice in real-time with 400+ realistic AI voices and 100,000+ sound effects.
- Protect your privacy by changing your voice or have fun by sounding like your favorite Vtuber, anime character, or celebrity.
- Enjoy zero-delay voice changing for seamless, uninterrupted gameplay and streaming.
See What Influencers Have to Say about Our Tools
Why Choose iRocket

8 + Years
iRocket
1.2 + Million
Satisfied Customers

200 +
24/7

Trusted by Top-Tier Media Sites Worldwide